Spam Number Investigation Portal Is This Spam Number Explaining Verification Methods
A Spam Number Investigation Portal consolidates data on suspicious numbers, explaining verification methods and how signals are weighed. It emphasizes ID clues, call logs, and user reports, cross-checked with timestamps and patterns. The approach prioritizes traceable evidence while protecting privacy. Results reveal red flags, credibility, and safety steps, guiding users toward informed decisions. The framework hints at complexities behind classifications, inviting further scrutiny and a closer look at how data supports conclusions.
What Is a Spam Number Investigation Portal and Why It Helps
A Spam Number Investigation Portal is a centralized resource that aggregates, analyzes, and verifies details about phone numbers linked to spam or fraudulent activity. It frames how spam numbers are tracked across investigation portals, establishing standards for verification methods. By examining call logs and related data, it reinforces privacy safety while empowering users to assess risk, respond intelligently, and maintain personal autonomy.
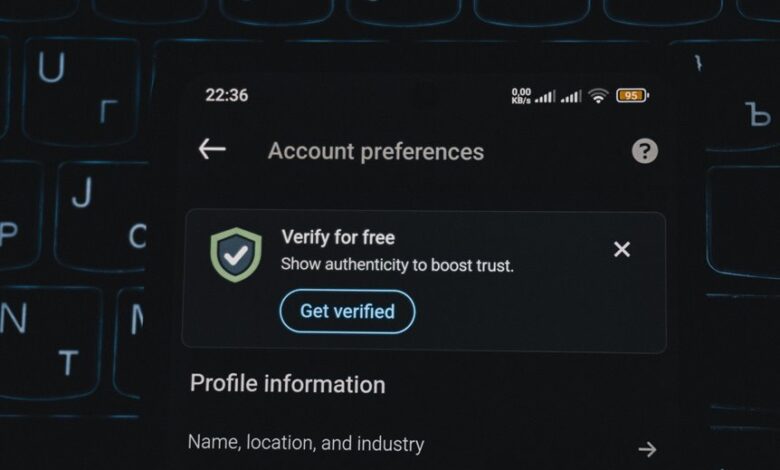
How Verification Methods Actually Work (ID Clues, Call Logs, and Reports)
Verification methods underpin how a Spam Number Investigation Portal validates claims about suspect numbers, using distinctive ID clues, call logs, and user-generated reports to assign credibility and risk levels. The system cross-references identifiers, timestamps, and patterns, translating evidence into structured assessments. Verification methods prioritize traceable data, while call logs illuminate call frequency, duration, and destinations, guiding informed risk stratification.
Interpreting Results: Red Flags, Legitimacy, and Safety Steps
Interpreting results from the Spam Number Investigation Portal centers on distinguishing credible signals from misleading indicators. Analysts assess spam patterns, corroborate with diverse data sources, and separate noise from fact. Red flags include inconsistent reports and dubious provenance; legitimacy stems from verifiable origins and transparent methods. Safety steps emphasize privacy protection, cautious outreach, and documented procedures to minimize exposure to suspicious numbers.
Protecting Your Privacy and Staying Compliant While Investigating Numbers
Protecting privacy and maintaining compliance are essential when investigating numbers, as rigorous safeguards minimize exposure to sensitive data and uphold legal and ethical standards. The approach emphasizes disciplined privacy practices and robust data handling, supporting transparent audits. Wariness checks calibrate scrutiny, while risk assessment identifies exposure points, guiding remediation. This detached framework clarifies responsibilities, reduces harm, and preserves freedom through accountable, lawful inquiry.
Conclusion
The Spam Number Investigation Portal, in its sober, data-driven fashion, delivers conclusions with the gravity of a courtroom verdict and the poise of a librarian. Its verification methods—ID clues, call logs, and user reports—are presented as airtight evidence, leaving little room for whimsy. Yet the satire lurks: a system built to tame chaos must trust noisy inputs, while privacy safeguards politely remind us that truth comes with a docket. In short, numbers lie—carefully.




